The dark web is a part of the internet that is not indexed by traditional search engines, making it a haven for various activities, both legitimate and illegal. Accessing the dark web can seem daunting due to its reputation and the complexities involved. However, understanding how to navigate it safely and responsibly is crucial for anyone interested in exploring its depths.
Access Dark Web
Common software packages used for this purpose include I2P, Freenet, and The Onion Router (Tor). Because the Dark Web is sometimes used for illicit activities, it receives far more publicity than the rest of the Deep Web. These programs follow hyperlinks from one webpage to another, recording the address of every webpage they access. While the size of the Deep Web cannot be measured, experts estimate that the Deep Web is much larger than the surface internet. While it provides strong privacy protections, it is also exploited for illegal transactions, including drugs and other contraband.
This guide explores how to access the dark web safely on different devices while also covering both the benefits and risks of delving into this part of the internet. As the dark web continues to grow, safe access to dark web sites matters more than ever. Users should choose engines based on their need for anonymity, speed, comprehensiveness, or research-focused features. Ahmia emphasizes legal content filtering, DuckDuckGo prioritizes privacy without tracking, NotEvil covers extensive indexing of forums and marketplaces, while Haystak offers advanced filtering and historical snapshots.
To access the dark web, users typically employ specialized software, with Tor (The Onion Router) being the most commonly used tool. Tor allows users to surf the web anonymously by routing their connection through a series of servers, obscuring their IP address. This anonymity is what attracts many individuals to the dark web, whether for privacy reasons, whistleblowing, or exploring its various hidden services.
Setting Up Your Access
- As a result, law enforcement has employed many other tactics in order to identify and arrest those engaging in illegal activity on the dark web.
- The default Tor search engine is a dark version of DuckDuckGo, but there are other dark web search engines you can use on Tor.
- It is used to maintain the privacy and anonymity of online activity, which is useful for both authorized and illegal purposes.
- Fresh Onions constantly crawls the dark web to discover and map new onion services as they appear.
- If you use the Tor browser to access a standard website, it offers protection and anonymity to users — they pop into the Tor cloud, that "onion space", and pop back out virtually elsewhere, with their identity and location obscured.
First, download the Tor Browser from the official Tor Project website. It's essential to ensure that you're only using legitimate sources to avoid malware or security risks. Once installed, you can launch the browser, which looks similar to traditional browsers but is configured to access hidden services on the dark web. Remember, while browsing, it’s vital to avoid revealing personal information, as this can compromise your anonymity.

Exploring Dark Web Sites
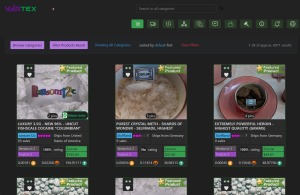
Unlike the surface web, dark web sites have domains that end in .onion. These sites can offer a range of content from forums and marketplaces to blogs and whistleblower platforms. While some of these sites host illegal activities, others serve more benign functions, such as providing information on privacy and security. Exercise caution and always verify sources before engaging with any content.
- Dark web browsers such as Tor are designed to offer anonymity and access to hidden services not listed by standard search engines.
- These dark web commerce sites are often powered by cryptocurrency, so the users can shroud their purchases in purported anonymity.
- Since dark web marketplaces or forums are often monitored by law enforcement, it can be difficult to distinguish between criminal actors and good faith investigators.
- So not only is your web activity hidden by Tor, but you can also mask your IP address for other network processes by connecting via a range of global VPN server locations.
Security Precautions
While accessing the dark web, it’s crucial to employ strategies to safeguard your security. Use a reliable VPN in conjunction with the Tor browser to add an extra layer of security. Additionally, refrain from using your real identity, and consider creating a separate email account specifically for dark web interactions. Keeping your activities private is essential, as the dark web can be a risky environment.
Legal Implications
Engaging with the dark web does come with legal considerations. While merely accessing the dark web is not illegal, many activities conducted there are against the law, including but not limited to purchasing illicit drugs, firearms, or stolen data. Being aware of the laws in your country is critical to avoid potential legal issues.
Conclusion
Accessing the dark web can provide unique insights and opportunities, but it's essential to approach it with caution and awareness. By using the right tools and strategies, individuals can explore this hidden part of the internet safely. Always prioritize your security, respect the law, and remember that the dark web is a double-edged sword, capable of both positive and negative outcomes.