The dark web is a hidden part of the internet that is not indexed by traditional search engines. It is often associated with illegal activities, but it also serves as a platform for privacy-focused individuals and activists seeking to communicate anonymously. Accessing the dark web requires specialized tools and an understanding of its structure, which can be daunting for those unfamiliar with this shadowy realm of cyberspace.
- The dark web intentionally anonymizes users, while the deep web does not.
- For users who want a stable and proven anonymity solution, it remains the strongest overall choice.
- The next decade saw Tor becoming a significant tool for online anonymity and allowing users to access websites on the ‘dark net’, where dark web content now exists.
- The deep and dark web are applications of integral internet features to provide privacy and anonymity.
- Each version of the dark web provides its own dataset, encryption services and risks from attempting to access it.
Lost credentials or overly restrictive systems can hinder legitimate use, a trade-off for security. The Deep Web’s design prioritizes privacy, inherently limiting accessibility. The dark web deep web difference is primarily in their accessibility methods and intended purposes. When examining what is dark web used for, we find both legitimate privacy protection and unfortunately, a range of illicit activities. Privacy-focused communications, whistleblowing, secure journalism, and individuals under restrictive regimes requiring anonymity Many wonder if the dark web is easily accessible?
Accessing The Dark Web
ZeroFox monitors paste sites, hacker forums, hidden communication channels, TOR services, and thousands of other deep and dark web sources to detect, disrupt, and dismantle cyberattack infrastructure. All password-protected content is part of the deep web, including financial accounts, secure databases, webmail accounts, and subscription websites. Content on the deep web includes private intranets, private member sites, public and private databases, and many other types of hidden content. Law enforcement agencies worldwide monitor the dark web for illegal activities, such as the trafficking of illegal drugs, weapons, and stolen data.
Silobreaker puts the widest range of threat intelligence in one place, automatically collecting and analyzing data from millions of sources, including those on the open, deep and dark web. Using natural language processing and machine learning, Silobreaker extracts meaningful insights from dark web data. Silobreaker aggregates data from various sources on the dark web, including forums, marketplaces, chat rooms, and social media platforms.
To begin accessing the dark web, you need to download the Tor Browser, a specialized web browser designed to protect user privacy and security. Tor, short for The Onion Router, obscures your internet traffic by routing it through multiple volunteer-operated servers before reaching its destination. This process not only hides your IP address but also allows users to access .onion websites, which are exclusive to the dark web.
Setting Up the Tor Browser
Once you have acquired the Tor Browser, install it as you would any other program. After installation, launch the browser and connect to the Tor network. Keep in mind that while the Tor Browser offers anonymity, it does not guarantee complete security. Users should always remain vigilant and follow best practices when accessing the dark web.
Exploring Dark Web Websites
When exploring the dark web, users may encounter various sites, some of which require specific links to access. These links are often shared in dark web forums or via encrypted communication channels. To enhance your security, consider using a Virtual Private Network (VPN) alongside the Tor Browser. This layering of security measures contributes to a safer experience while accessing the dark web.
- Just because you can’t get there by popular search engine doesn’t automatically make it nefarious.
- While the Tor browser offers anonymity, users seeking maximum privacy often add a Virtual Private Network (VPN) for extra security.
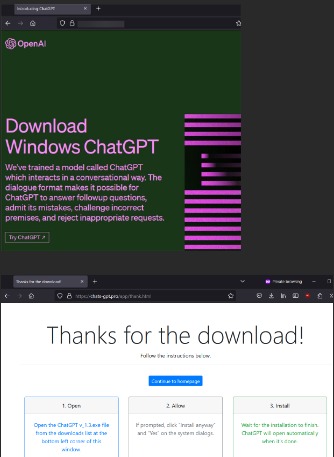
- Using the wrong browser exposes you to risks that hidden services often exploit to identify or target visitors.
- Onion Search engine offers a smooth experience to its users and allows access to thousands of hidden services.
- There are at least some real and fraudulent websites claiming to be used by ISIL (ISIS), including a fake one seized in Operation Onymous.
Maintaining Anonymity
Prior to accessing the dark web, it's essential to understand that anonymity is key. Avoid providing any personal information or engaging in activities that can expose your identity. Additionally, utilizing cryptocurrency for transactions is common practice, as it offers another layer of anonymity that traditional payment methods do not provide.
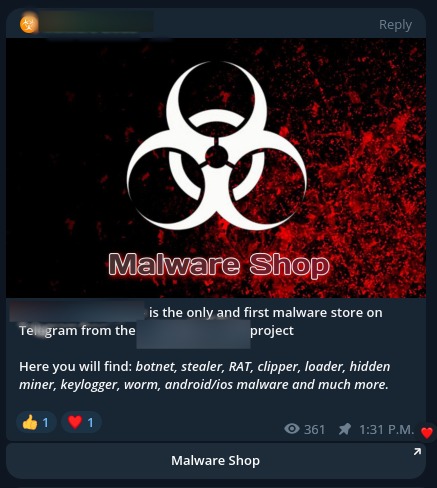
Risks Involved
While accessing the dark web can be thrilling, it is accompanied by significant risks. Users may encounter scams, illegal content, or even malicious software. It's crucial to navigate with caution and have an understanding of the legal implications of engaging in certain activities, as law enforcement agencies actively monitor the dark web.
Conclusion
Accessing the dark web presents both opportunities for anonymity and risks that users must acknowledge. By utilizing tools like the Tor Browser and maintaining awareness of potential threats, individuals can explore this hidden digital landscape responsibly. Remember to follow safe practices and prioritize your security when venturing into the depths of the dark web.