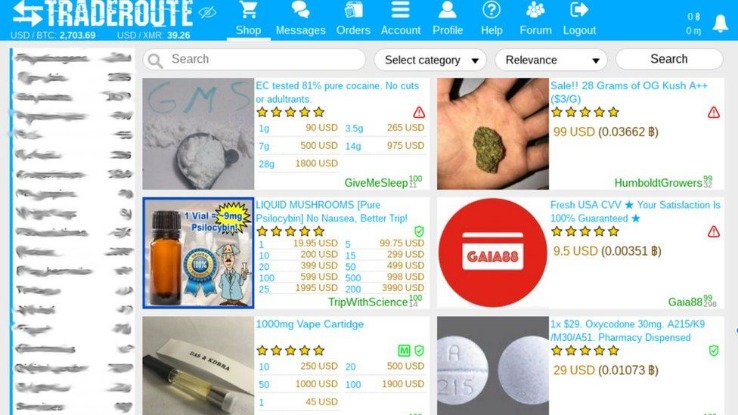
For example, they might claim to have stolen more impressive datasets than they really have in an attempt to drum up business, pressure victims or seem more accomplished. Many marketplaces feature review systems, and some offer escrow services to help ensure people get paid. Cybersecurity pros watch these forums, too, to keep tabs on the cyberthreat landscape. Most dark web marketplace transactions use cryptocurrencies such as bitcoin to preserve the anonymity of buyers and sellers. There are even some escrow services and rating systems, but these systems are often gamed by the sellers.” The dark web intentionally anonymizes users, while the deep web does not.
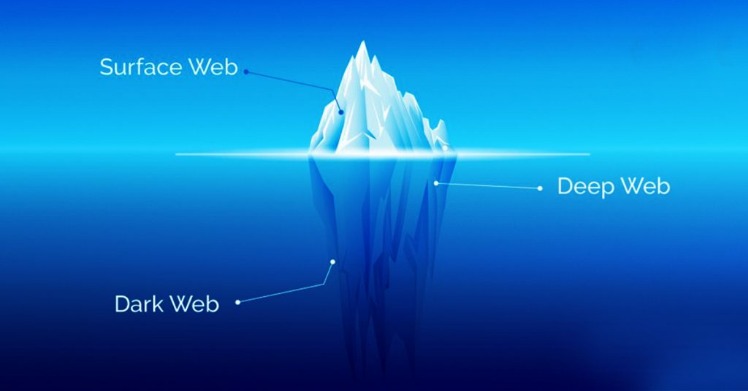
The dark web is a part of the internet that is not indexed by search engines and requires specific software to access. It is often associated with illegal activities, but it also serves as a platform for privacy-focused communication and information exchange. This article explores how individuals can access the dark web, the tools required, and the implications of venturing into this shadowy realm.
- There exists a considerable danger of identity theft, underlining the importance of utilizing tools that monitor the dark web to ensure the protection of personal information.
- By integrating Dark Web monitoring into their security strategies, organizations can stay ahead of threats and ensure the safety of their data and systems.
- To most users, the internet is what they experience through their email client and web browser every day, but there are a number of expansive services that operate in the background and the “web” is just one part of it.
- Scott Dueweke the president and founder of Zebryx Consulting states that Russian electronic currency such as WebMoney and Perfect Money are behind the majority of the illegal actions.
- Implement the best security and compliance solution for Microsoft 365.
Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. And with many unfamiliar-looking sites on the dark web, it’s harder to distinguish safe websites from shady ones, and easier to fall victim. By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. It’s possible to buy and sell illegal drugs, malware, and prohibited content in darknet marketplaces.
- The dark web is located at probably the most profound level of the internet, only reachable through specific software like The Onion Router (Tor).
- Improve the speed, accuracy and productivity of security teams with AI-powered cybersecurity solutions.
- Browsing the dark or deep web in 2026 is safer than in previous years, but only when you understand the risks that come with hidden networks.
- Users need specialized software, like the Tor Browser, to access the dark web.
- Because visitors can remain anonymous, it is useful for cybercriminals who want to take part in illegal activities.
- This content isn't hidden for malicious reasons—it's simply private and requires authentication to access.
Access To Dark Web
Gaining access to the dark web requires a series of steps and a healthy dose of caution. Here’s how to get started:
Whonix was introduced in 2012 as a distribution designed to separate network traffic from user activity. Its distributed architecture encrypts and splits data into fragments stored across volunteer nodes. Freenet was introduced in 2000 as a research project aimed at building a censorship-resistant information network.
Steps to Access the Dark Web
- Download Tor Browser: This is the most common method to access the dark web. The Tor Browser anonymizes your connection and enables you to visit .onion websites.
- Install a VPN: While Tor provides anonymity, using a Virtual Private Network (VPN) adds an extra layer of security by masking your IP address.
- Ensure Security: Before accessing, make sure your system is protected with antivirus software and that your operating system is up to date.
- Understand Risks: Be aware of the potential dangers such as data theft, scams, and illegal content that may be encountered.
What You Can Find on the Dark Web
- Illicit Goods: The dark web is notorious for marketplaces selling drugs, weapons, and stolen data.
- Privacy-Focused Forums: There are communities focused on free speech and privacy, discussing various topics without censorship.
- Torrents and File Sharing: Users can share files that may not be available on the mainstream web.
Potential Risks of Accessing the Dark Web
While the dark web has legitimate uses, it also harbors numerous threats. Consider these risks:
- Legal Issues: Engaging in illegal activities can lead to severe legal repercussions.
- Malware Exposure: Numerous sites may host malware that can infect your system.
- Scams: Many transactions can be fraudulent, leading to loss of funds or personal data.

FAQs About Accessing the Dark Web
1. Is accessing the dark web illegal?
No, accessing the dark web itself is not illegal. However, engaging in illegal activities on it can lead to serious legal consequences.
2. Do I need special skills to access the dark web?
No special skills are required, but basic computer knowledge and understanding of internet safety are essential.
3. Can I be traced on the dark web?
While Tor provides anonymity, it is not foolproof. Engaging in risky behavior can increase the chances of being traced.
4. Are there any safe areas on the dark web?
Yes, some parts focus on privacy advocacy, journalism, and safe communication, but caution is always advised.
In summary, accessing the dark web involves using specific tools like the Tor Browser and VPNs while remaining aware of the associated risks and regulations. Whether for legitimate reasons or curiosity, understanding how to navigate this hidden part of the internet responsibly is crucial.